About Pierre Le Stunff

Pierre Le Stunff is an IT leader with strong experience in enterprise architecture. He notably worked at Fortuneo, where he rose through the ranks to become CTO. In that role, he led a team of over 30 people and oversaw key projects, including the management and security of banking data, the improvement of customer journeys, and the governance of sensitive data. In 2023, Pierre became Lead Enterprise Architect, tasked with supporting the digital transformation of the industrial sector. He helps the group’s various business units leverage digital technologies and artificial intelligence to optimize production processes and strengthen their competitiveness. With a strategic vision and recognized expertise, Pierre Le Stunff is capable of tackling complex challenges and delivering innovative solutions tailored to the needs of large enterprises.
CTO Fortuneo
Enterprise architects : 7 Keys to connecting IT and business
I’ve been working with Enterprise Architects for 15 years, and to help all of us gain more visibility (and influence!), I’ve prepared seven simple and essential “keys”. Yes, some of them might seem obvious, but they’re worth repeating as a group: these principles can truly make a difference in the field when trying to align IT and business.
Let’s be honest: in large companies, driving a successful digital transformation is a bit like solving a puzzle with pieces that don’t all seem to come from the same box. IT and business are often two worlds with different priorities, different work rhythms, and communication that rarely flows smoothly. You know that scene where everyone’s talking, but no one really understands each other? That’s exactly where the Enterprise Architect becomes essential.
As mediators, EAs work to close those gaps and create real synergy between technology and business. In this article, you’ll find strategies and methods to help you connect IT and business effectively.
Understanding the gaps between IT and Business
Before hoping to build a connection between IT and business, we first need to understand why this gap exists. Here are three common reasons why things often get stuck.
Mindset differences : On the business side, it’s all about speed, agility, and flexibility. IT, on the other hand, is focused on quality, security, compliance, and reliability. In short, each side has its own priorities, and this mindset gap is the root of many misunderstandings. Business moves fast, and IT slows things down, both for good reasons, but not the same ones.
Project experience : IT teams have often adopted a project methodology. We live project, breathe project, eat project. On the other side, some business units may go years without any major projects, operating on much longer strategic cycles. As a result, there’s often a disconnect in how projects are approached and understood.
Limited communication : You’d think speaking the same language would solve everything, but IT teams often have their own jargon, and decoding it quickly becomes a challenge for business teams. The reverse is true as well. The result: collaboration gets complicated, and making shared decisions becomes a real challenge.
7 keys to excelling as an IT architect
Here are seven essential rules for excelling as architects and strengthening the connection between IT and business. No magic potions here, just simple principles that, when applied properly, can truly transform the dynamic.
1. Define (but not alone) the founding principles

To create true synergy between IT and business, it’s essential to jointly define founding principles that will guide all decisions. These principles must be clear, shared by all teams, and, above all, reflect both technical needs and business objectives. Here are some examples of guiding principles that Enterprise Architects can use to facilitate this alignment:
- Be clear on your business goal : Every IT project must be aligned with a specific business objective.
- Choose a predominant public cloud partner : Facilitating cloud adoption to accelerate innovation.
- Agree on your security objectives : Put security at the center of all IT initiatives.
- You build it, you support it : Encourage IT team responsibility across the entire systems lifecycle.
- Trust, but verify : Establish a culture of trust, but ensure that objectives are met.
- Keep It Simple Stupid (KISS) : Simplify processes as much as possible to avoid unnecessary complexities.
These principles, which you can select and adapt, help clarify expectations and guide decision-making across all teams, from development to governance. They support transformation while anchoring IT culture around shared values, facilitating alignment with business objectives.
For example, I used the law of the instrument (Maslow’s Hammer) to highlight the interest and posture to adopt during a cloud transformation program. The idea was to break away from usual patterns and allow the company to avoid reproducing the same practices in the cloud as on their own infrastructures.
In each of your interactions with your stakeholders, you will be able to adhere to the principles you have agreed upon together, whether they are based, for example, on customer obsession, quality, or safety. This is an excellent lever for convergence with your contacts and consistency in your architectural instructions.
2. Facilitate the relationship between IT and the business
The primary role of an enterprise architect is to act as a bridge between IT and the business. This requires proactive communication, training in facilitation techniques, encouraging discovery, developing a network, and adopting a facilitative approach.
- Stance : The architect must actively participate in discussions to strengthen their legitimacy and credibility. This includes asking relevant questions, proposing solutions, and being a key player in decision-making.
- Learn Facilitation Techniques : Familiarizing yourself with methods such as Event Storming, Domain-Driven Design (DDD), Design Thinking, or graphic facilitation allows you to effectively structure and guide discussions.
- Encourage Discovery : Foster a structured approach that encourages stakeholders to identify their own role in the transformation. This can be done through co-creation workshops, brainstorming sessions, or role-playing exercises.
- Develop your Network : Surround yourself with experts and build an internal or external network to enrich your perspectives and your influence in the transformation process.
- Work closely with teams : As an architect, your role is to facilitate transformation, not impose it. Encourage the participation of all teams (development, operations, marketing, etc.) from the beginning of the process. This will allow you to gather diverse ideas and build solutions that meet the needs of the entire organization.
- Apply the Strangler Fig concept : This approach involves gradually replacing legacy systems with new solutions. By adopting this method, you demonstrate respect for existing systems while allowing for a smooth and gradual transition. This requires open communication and ongoing engagement with all stakeholders.
By adopting a facilitative and structured approach, you strengthen your position as an enterprise architect and encourage stakeholder buy-in to transformation projects. Get support and don’t go it alone in this type of approach.
3. Rely on fundamentals: Perspectives, Frameworks, User-centeredness
For an effective architecture, it is crucial to take a step back and rely on structuring tools :
- Create a tool catalog : Create a set of templates (BMC, SWOT, Roadmap, Eisenhower Matrix, etc.) to structure your thinking and projects. This will facilitate communication and understanding between stakeholders.
- Connect with frameworks : Use frameworks like the Cloud Adoption Framework to guide your initiatives. These tools provide solid foundations and best practices, simplifying co-construction with stakeholders.
- Bring new perspectives : Provide stakeholders with relevant insights into their concerns, which can strengthen the relevance of your architectural proposals.
- Adopt a user-oriented approach : By taking a step back and using appropriate tools, you facilitate the structuring of your projects and encourage stakeholders to support your vision.
4. Adapt your posture according to the interlocutors (without falling into demagogy)
The relevance of an enterprise architect comes, among other things, from connecting the different perspectives of the company and bringing a comprehensible vision of the IS to all levels of the company.
Voici quelques stratégies clés :
- Understand your audience : Identify the priorities and motivations of each stakeholder (CEO, CISO, CTO, etc.) to tailor your pitch and address their specific concerns.
- Assess organizational culture : Analyze whether the company is conservative or progressive and adjust your approach accordingly.
- Map decision-making structures : Familiarize yourself with the decision-making bodies and the power of influence of each actor. This will help you better structure your proposals and anticipate reactions. You will learn a lot, as an architect, to work and structure the sociogram of the organization, structures and restructurings (reorg), M&A in order to project their impacts on IT systems (obsolescence, increase in TCO, cyber risks).
- Apply the Reverse Conway Maneuver : Use this technique to align the target architecture with organizational needs, while remaining discreet about its use. This will allow you to address many aspects of the transformation, such as the target architecture, the Target Operating Model, the transformation plan, and the master plan.
- Put your ego aside (or pretend to) to adopt a posture of humility and collaboration : Putting your ego aside and adopting a posture of humility are crucial elements for an enterprise architect. By putting user needs first and fostering collaboration, you can build information systems that not only meet technical requirements but also support the organization’s strategic objectives.
By adapting your posture and your speech according to the contexts and the interlocutors, you reinforce your legitimacy and encourage support for your architectural vision.
5. Excel in IT governance
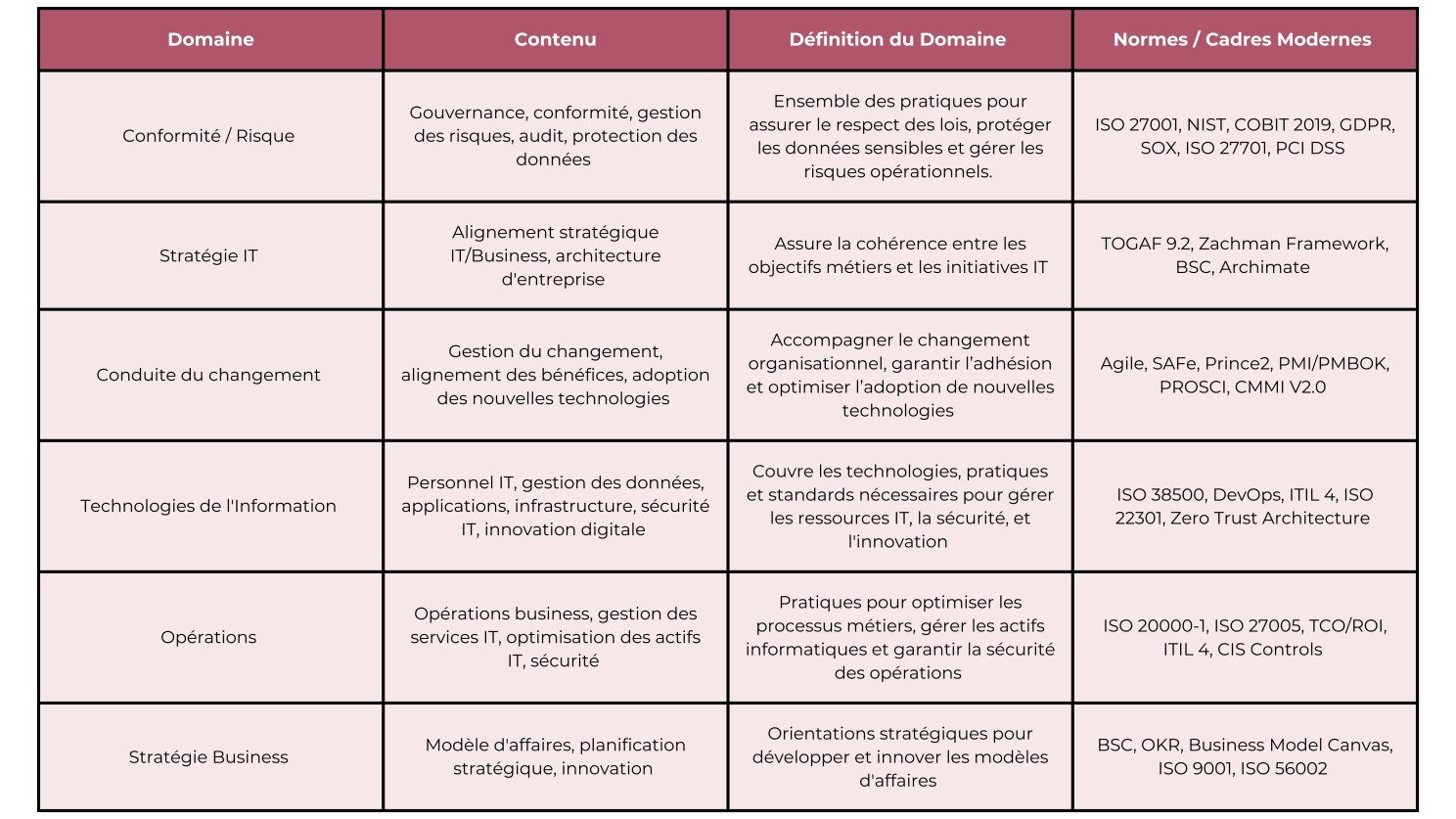
Executives know that IT governance is a key lever. They expect architects to align IT with business objectives, enhance agility, and minimize risk. Here’s a table that outlines the new IT governance requirements with modern standards and frameworks :
6. Popularize IT concepts and main components of IS
As an enterprise architect, you collaborate with many departments within the organization. Simplifying the understanding of IT concepts and establishing a common vocabulary is crucial for successful transformations within IT teams and beyond. Here are some examples of key components and concepts of a modern IT system that are essential to understand and communicate within the enterprise:
Data Architecture and Governance
1. Data in Transit:
- Data Streaming: Continuous transmission of data (Kafka, Apache Pulsar).
Messaging: Messaging systems for asynchronous communication (RabbitMQ, Apache ActiveMQ). - Queuing: Queue management for delayed processing (AWS SQS, Azure Queue Storage).
2. Data at Rest:
- Data Lake: Reservoirs of unstructured or semi-structured data (AWS S3, Azure Data Lake). A Data Lake is a digital “lake” where all company data is centralized, regardless of its form or structure. It offers immense flexibility for storage and analysis, but requires rigorous management to extract maximum value from it. It is a key technology for companies wishing to make the most of their data and remain competitive in the era of Big Data. This allows you to introduce concepts around data governance or MDM (Master Data Management) to avoid the creation of a data swamp.
- Data Mesh: A decentralized data management model, aimed at distributing data responsibility to each domain.
- Data Warehouse: Data warehouses for structured analyses (Snowflake, Google BigQuery, Amazon Redshift).
- Data Mart: Specialized subsets of data warehouses for specific needs (e.g., finance, marketing).
Object Storage: Unstructured data storage (AWS S3, Azure Blob Storage). - Databases: Relational and NoSQL database management systems (PostgreSQL, MySQL, MongoDB, Cassandra).
3. Data Security:
- Encryption: AES, RSA to secure data in transit and at rest.
- DLP (Data Loss Prevention): Solutions to prevent data leaks or loss (Symantec DLP, Microsoft 365 DLP).
Network and Connectivity
1. Network:
- SD-WAN (Software-Defined WAN): Network solution for dynamically managing connections between sites via cloud services.
- VLAN (Virtual LAN): Logical segmentation of a physical network to improve security and management.
- LAN (Local Area Network): Local network for connecting devices within a limited geographical area.
- VPN (Virtual Private Network): Tools for securing remote connections and encrypting data (OpenVPN, IPsec).
2. API Management:
- API Gateway: Centralized entry point for managing APIs (Kong, AWS API Gateway).
- Rate Limiting, Authentication, Monitoring: Controls applied to APIs to manage access and ensure their availability.
IT Infrastructure and Hosting
1. Computing:
- Virtualization: Running virtual environments on a single physical machine (VMware, Hyper-V).
Containers: Containerization of applications for isolation and portability (Docker, LXC). - Orchestration: Managing containers at scale (Kubernetes, OpenShift).
Serverless Computing: Running code without managing server infrastructure (AWS Lambda, Google Cloud Functions).
2. Storage and Hosting:
- Persistent Storage: Data storage that persists even after an application is stopped (Amazon EBS, Google Persistent Disks).
Static Web Hosting: Hosting static applications or websites (Netlify, GitHub Pages). - CDN (Content Delivery Network): A network of geographically dispersed servers to accelerate content delivery (Cloudflare, Akamai).
IT Security
1. System Security:
- SOC (Security Operations Center): Center dedicated to monitoring security incidents in real time.
- SIEM (Security Information and Event Management): Security log and event management platforms (Splunk, IBM QRadar).
2. Security Testing:
- SAST (Static Application Security Testing): Source code analysis to identify vulnerabilities (Checkmarx, Veracode).
- DAST (Dynamic Application Security Testing): Analysis of running applications to identify vulnerabilities (OWASP ZAP).
- IAST (Interactive Application Security Testing): Real-time interactive testing to monitor for abnormal behavior (Contrast Security).
3. Observability and Monitoring:
- Observability: Monitoring of IT system status, metrics, and logs (Prometheus, Grafana, Datadog).
- AIOps (Artificial Intelligence for IT Operations): Using AI to automate incident management and log analysis (Moogsoft, Splunk AIOps).
Application and Systems Management
1. Enterprise Systems:
- ERP (Enterprise Resource Planning): Integrated management systems for enterprise resources (SAP, Oracle ERP).
- PLM (Product Lifecycle Management): Product lifecycle management, from design to production (Siemens Teamcenter, Dassault Systèmes).
- CRM (Customer Relationship Management): Customer relationship management (Salesforce, Microsoft Dynamics).
- EDM (Electronic Document Management): Tools for managing and storing electronic documents (Alfresco, OpenText).
2. Device and Infrastructure Management:
- MDM (Mobile Device Management): Centralized management of mobile devices (AirWatch, Microsoft Intune).
- CMDB (Configuration Management Database): Database for tracking IT assets and their relationships (ServiceNow, BMC Remedy).
- Lifecycle Management: Application lifecycle management (from planning to retirement).
DevOps and infrastructure as code
1. Infrastructure as Code (IaC):
- IaC: Infrastructure management and provisioning through code (Terraform, AWS CloudFormation).
- Automation: Automation tools for deployment and management (Ansible, Puppet, Chef).
2. CI/CD (Continuous Integration / Continuous Deployment):
- CI/CD Pipelines: Automation of continuous integration and application deployment (Jenkins, GitLab CI, CircleCI).
- Test Automation: Automated tests to ensure code quality throughout the development lifecycle (Selenium, TestNG).
Web concepts and protocols
1. OSI Protocols and Models:
- OSI Model: A 7-layer framework for standardizing network communications (physical, data link, network, transport, session, presentation, and application layers).
- TCP/IP: A model used for Internet communication, the basis of modern network protocols.
- HTTP/2, WebSockets, gRPC: Communication protocols used for APIs and the web.
- OAuth 2.0, OpenID Connect: Authentication and authorization protocols.
2. Web Concepts:
- CMS (Content Management System): Systems for managing and publishing web content (WordPress, Drupal).
- Microservices: Service-oriented architecture for modular and scalable applications.
- REST, GraphQL, gRPC: Protocols for interaction between services (APIs).
3. Programming Languages:
- Backend: Java, Python, Go, C#, Rust.
- Frontend: JavaScript (React, Angular, Vue), HTML, CSS.
7. Cultivate a personal style
Your personal style is your signature! Be authentic, attentive to your audience, and take care in how you express yourself. This authenticity will build trust and support among your colleagues.
Conclusion
Connecting IT to business goes far beyond technical choices; it’s a collaborative effort and ongoing communication. By defining clear principles, facilitating exchanges, and relying on concrete approaches, you can help stakeholders understand the value of the architecture for the organization.


